There is a quote that I often misquote saying, “The only truly secure system is one that is powered off”. This was said by Gene Spafford. Of course, there’s more to that quote. The thing is, no matter what we do, it seems a useful computer will never be truly secure. This even goes for our phones. Even when using apps with end-to-end encryption, data can still be obtained through a push notification.
Why didn’t we know?
Apparently, put under some sort of gag order, Apple has, for some time, received requests for notification data. Oh, don’t worry, Google has been doing the same. But, for some reason, the US government has kept Apple and Google from saying anything. This is why you’re hearing about it now. Apple has not been able to even put it in their transparency reports.
So, why are we hearing about it now? US Senator Roy Wyden was tipped off. He’s a part of the Senate intelligence committee and this is what he had to say:
In the spring of 2022, my office received a tip that government agencies in foreign countries were demanding smartphone “push” notification records from Google and Apple. My staff have been investigating this tip for the past year […]
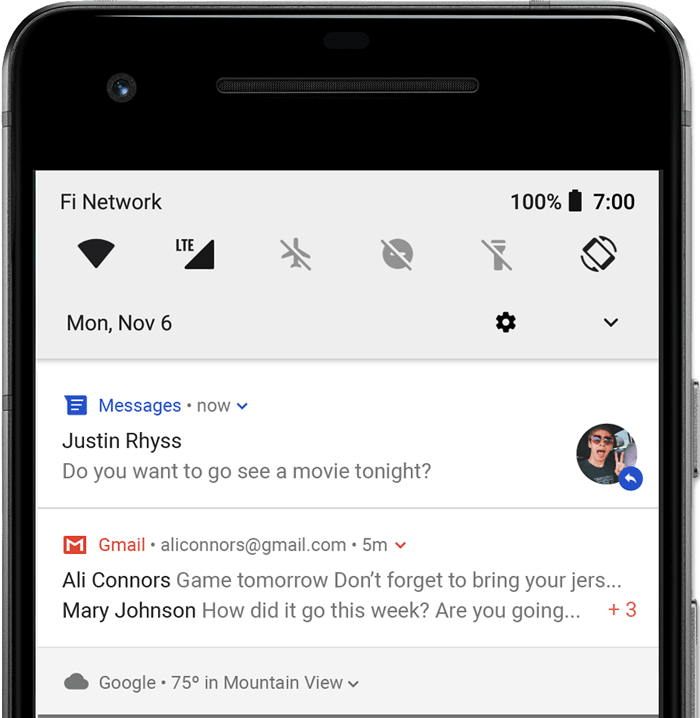
Push notifications […] aren’t sent directly from the app provider to users’ smartphones. Instead, they pass through a kind of digital post office run by the phone’s operating system provider. For iPhones, this service is provided by Apple’s Push Notification Service; for Android phones, it’s Google’s Firebase Cloud Messaging. These services ensure timely and efficient delivery of notifications, but this also means that Apple and Google serve as intermediaries in the transmission process.As with all of the other information these companies store for or about their users, because Apple and Google deliver push notification data, they can be secretly compelled by governments to hand over this information.”
When he reached out to the two companies, both hit him back saying that the information was “restricted from public release” by the US government.
This then prompted Sen. Wyden to send an open letter to the US Department of Justice, asking them to remove the restriction:
Apple and Google should be permitted to be transparent about the legal demands they receive, particularly from foreign governments, just as the companies regularly notify users about other types of government demands for data. These companies should be permitted to generally reveal whether they have been compelled to facilitate this surveillance practice, to publish aggregate statistics about the number of demands they receive, and unless temporarily gagged by a court, to notify specific customers about demands for their data. I would ask that the DOJ repeal or modify any policies that impede this transparency.”
Sen. Roy Wyden
Apple tells all
This sprung a trap Apple needed to start spilling the tea on the whole thing.
In this case, the federal government prohibited us from sharing any information,” the company said in a statement. “Now that this method has become public we are updating our transparency reporting to detail these kinds of requests.”
Apple statement to Reuters
How bad is push notification spying?
Now, remember back in the PRISM days when people were talking about metadata. Push notifications are like the new “metadata” with this situation.
Essentially, while governments can’t necessarily see messages that are being sent via push notifications, lines could be drawn. Ordered a Lyft lately? It might reveal location information if a message was sent from the driver. What about food? If you order from your favorite hole in the wall restaurant, that gives up an approximate location.
But here’s a big one. While they can’t see messages being sent, it could reveal who you were having conversations with and how. Were you at a protest last night? Well, if you had your phone on you, they know you were there. They can request your notifications to see who you may have been messaging back and forth. They can then take that info and start connecting the dots to see who all was there. Just by seeing their notifications and start creating webs.
It isn’t that hard to see how this could get out of hand. Luckily, now that the lid has been removed, we can see how often and who is making these requests. Sadly, we still won’t know against who.
Source: 9to5Mac